NotMyHomelandNE+
For Tyler. Some protocols require encryption offline.
I now operate like a systems administrator protecting classified data from a nation-state adversary. Every potential confidant undergoes rigorous penetration testing; I watch how they handle others' secrets like monitoring their privilege escalation techniques, test their responses to progressively sensitive information as if deploying honeypots, analyse their digital footprint of emotional intelligence for indicators of compromise. To my own detriment at times, I've constructed concentric circles of access controls around this particular memory. Permitting a few the privilege to glimpse the incident headers but not the payload.
The fundamental problem is this: I do need to tell people.
This story has been sitting in quarantine too long, a critical vulnerability report gathering digital dust. It needs acknowledgement, a proper HTTP 200 response — but I'm so often receiving an immediate 403 forbidden response. Connection terminated before the SSL handshake even completes. I need a reliable endpoint with sufficient bandwidth and processing power to handle the payload without packet loss or system failure. I'm exhausted by these packets perpetually queued with nowhere to go.
The Critical Vulnerability Disclosure
The CVE requiring disclosure: a zero-day exploit that weaponised my entire digital and physical existence, executed as a public character assassination broadcast to hundreds of followers on Twitter and other places in the internet's dark underworld. This wasn't mere data exfiltration — this was the dismantling of my identity infrastructure, where my name, my address, my images, my cognitive coherence and social stability as an individual, my very essence as a functioning human entity was methodically dissected, distorted and reconstructed into malicious code for mass consumption.
What transpired defies conventional threat modelling where victims are complicit in their digital demise, the classic scenario of engaging with mindless trolls, clicking suspicious links, or voluntarily surrendering credentials. This was technology-facilitated abuse operating outside established security frameworks, a sophisticated attack vector that current defensive strategies hadn't anticipated. The variant I encountered was a passive surveillance nightmare: I became an unwilling observer as my existence, non-consensual images of me, my entire social ecosystem was systematically harvested and transformed into a public spectacle for others to analyse, evaluate and ultimately discard like obsolete hardware.
The attack chain reconstructed reads like a textbook advanced persistent threat: A malicious executable materialised in my physical living space, conducted extensive network reconnaissance, successfully traversed my personal and professional networks, hijacked my digital identity with precision, established persistent access across multiple platforms. He then repurposed my entire persona for sustained public consumption. The audacity was breathtaking — he didn't even attempt to sanitise the log files or cover his digital tracks.
As he brazenly tweeted, leaving evidence scattered across his timeline like a careless script kiddie:
There is nothing resembling a personal narrative about witnessing an abhorrent, fabricated version of yourself performing grotesque pantomimes on Twitter's stage, and giving encores in the gutters of the dark web. There is nothing intimate about receiving algorithmically amplified instructions to terminate your own existence. There is nothing private about executing an emergency evacuation from your home, your professional networks, your cherished friendships of seven years, all because a man you'd known for mere days decided to cast you as the primary antagonist in his unhinged psychological thriller, because Twitter.com granted him that right — plus a platform; that reach, that terrible power.
So no, I don't "have to" tell anyone this story.
But I am compelled to execute a data recovery operation on months of my life that were stolen, corrupted beyond recognition, and weaponised by the perfect storm of social media architecture, artificial intelligence amplification, and pure human malevolence. I do need to document precisely how I survived the deliberate expansion of my attack surface for his unhinged entertainment. Perhaps I have to explain so the same exploit vectors can't be deployed against you, so you can patch your own vulnerabilities before they're discovered and leveraged by the next predator scanning for unprotected targets in the network of human connection.
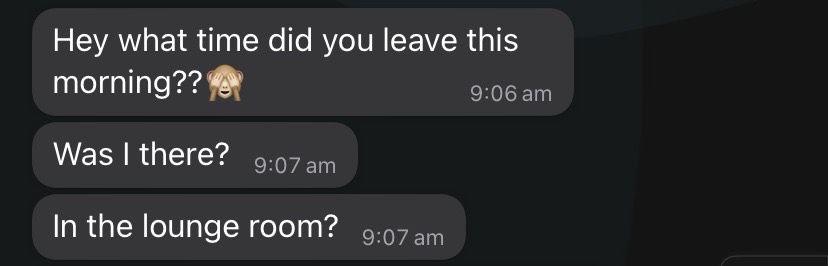
What time did you leave this morning?
The Persistent Malware of Memory…..(1) new message
Was I there?
In the lounge room?
The message crystallises against the fun wallpaper of a WhatsApp screen, persisting there like malicious code that's achieved kernel-level access to my operating system; a frozen MS365 PowerPoint presentation that won't Quit, stubbornly consuming system resources inside my mind. I lock onto it with the relentless focus of a debugging session going nowhere: I'm frantically attempting to close it, force-stop the process, deploy every conceivable CTRL-ALT-DELETE combination to cease it executing in the background.
This particular malware has maintained residence in my mind for twenty months since Brodie transmitted those packets of surveillance. Yet each morning brings a fresh boot sequence where these messages load automatically into active memory, corrupting my own reflection in the mirror like a persistent rootkit that's compromised my self-recognition protocols.
As I lie here in this anonymised room in Pandanus Reach, I recognise the necessity of conducting incident response. To trace the complete attack vector from that initial WhatsApp payload to where I am now, documenting the systematic compromise that occurred before I understood how thoroughly home networks could betray you, weaponised by those who share them.
I'm currently engaged in reverse-engineering my own source code of reconstructed identity, performing the singular function of rendering me as a viable person showing up in the world. Line by painstaking line, I'm recompiling a functional existence to replace the original that experienced a devastating breach by what security frameworks inadequately categorise as 'cyber abuse.'
The new version of me isn't flawless. There are clearly exit conditions from recursive loops that need immediate patching but overall… I'm developing exception handling for those inevitable moments when the primary instinct remains to silently vanish.
Vanish is what I did that September morning in 2023, when I climbed through my bedroom window and descended the external ladder at precisely 6:23 AM, a calculated risk mitigation strategy rather than face another potential encounter with Brodie in the lounge where he'd established his persistent monitoring station. After 10 days of constant texting, relentless demands for my attention — I'd had enough. To just disappear is what I've longed to do ever since a man I barely knew successfully violated my privacy and began broadcasting his unhinged character assassination of me across the surface internet and down into its darkweb sewer.
This pattern of strategic disappearance represents both survival protocol and systematic failure, the inevitable consequence of existing within a technological ecosystem where individual privacy constitutes merely optional configuration, where digital platforms grant unlimited administrative privileges to those who understand how to exploit the inherent vulnerabilities in human trust architectures.
Was any of it true? I mean true in the real world sense.
At first there were a couple of days of connection over shared interests that felt almost like friendship.
September 2023: The Initial Compromise
I lived a deliberately quiet existence in Canberra, maintaining stable network operations with a carefully curated rotation of housemates who came and went without triggering security incidents — well, a few minor breaches, but insignificant compared to the catastrophic system failure that Brodie would orchestrate.
I was happy. I had consistent routines, my voluntary research committee work at Brindabella University providing meaningful involvement with academic networks, my PhD remaining in maintenance mode and my employment in the research office ensuring financial security.
Time and accumulated wisdom were successfully executing healing protocols on those legacy vulnerabilities I'd previously classified as the most severe I'd ever encounter. How catastrophically wrong that threat assessment would prove to be.
Then the listing went up on Flatmates.com. It was September 13th, and an application arrived from Brodie, slipping through the email filter — it passed all surface-level authenticity checks, a perfectly crafted social engineering attack disguised as benign residential inquiry:
The communication protocols exhibited all the hallmarks of legitimate enquiry, no suspicious attachments, no obvious phishing indicators, no red flags that my analysis engines could detect. Just another career researcher seeking temporary access to Canberra accommodation.
He materialised within my laptop's display via Zoom. What appeared to me was a sophisticated and well-groomed macro in the form of a philosophy professor. There was certainly nothing nasty; salt-and-pepper hair — he resembled Hugh Grant. Fifty-two years old (according to transmitted metadata), articulate speech patterns suggesting advanced educational attainment, gentle demeanor deploying all recognised social signals of safety. Dr Brodie Lang — I've systematically altered his identifier, like every other data point that might enable reverse DNS lookup to factual coordinates — whose credentials successfully passed my initial verification subroutines. The Zoom session revealed absolutely nothing that my threat assessment recognised as… well… nasty. His background was clean, his references checked out, his presentation layer appeared entirely legitimate.
After all — the most dangerous exploits arrive wrapped in perfect authenticity, deployed by actors who understand exactly which trust protocols to manipulate. They don't announce themselves with obvious attack signatures or suspicious network traffic.
We talked easily for about 30 minutes and agreed he'd take a train to Canberra and could move in the following day. That's the thing about catastrophic breaches; they arrive so casually, as exactly what you're seeking, reliable, credible, safe — until they've slipped through a port you've left open and achieved administrative access to your most critical systems and begun their systematic destruction from within.
When he arrived with just one plastic bag and a backpack for a supposedly year-long stay, something in my subconscious noted the anomaly. But I'd learned to travel light too, understood the freedom of minimal possessions. I offered him a spare keep-cup, made jokes about his "charcoal executive" wardrobe, pressed grey pants and fitted black t-shirts that he wore like a uniform.
In those first days, there was an ease between us. We discovered shared interests; AI alignment ethics, religious extremism and philosophy, and anecdotally, we'd both resided briefly in China. He spoke of running for Senate in NSW, of being "radically secular," of having "made a lot of enemies in academia." I nodded along, respectful of his passionate conviction but it was hard to pin down his ideological views.
"We have so much in common," he said, leaning across the kitchen counter. "It's rare to meet someone who gets me."
I didn't get him though.
I was intrigued for sure. Looking back, I was still trying to figure him out. The words should have been a warning — how could he know what we had in common after seventy-two hours?
Here we observe the classical rapport-building methodologies of advanced social engineering attack. I failed to identify these techniques during real-time interaction. Social engineering initiates through systematic common ground establishment, trust protocol manipulation, creation of illusory connection architectures that bypass conscious security filters. I couldn't perceive how rapidly he was constructing a fictional version of me that existed exclusively within his own mind: a female character designed for a narrative he was simultaneously writing, one where I would execute functions I never consented to perform.
The authentic version of me, complex, mundane, flawed, possessing standard human vulnerabilities and inconsistencies, held no utility for his operational requirements. His system demanded alternative components: conspiracy frameworks, incel-themed betrayal narratives, an adversary sufficiently compelling to justify his persecution agenda and validate his victim-centric worldview. On reflection most unsettling was his absolute contempt for, and comprehensive unvarnished hatred for the female protagonists he ruminated over from his past.
Looking back, the warning signs were there from the beginning, scattered through the log files like breadcrumbs. The way he spoke about ex-girlfriends and his academic rivals with barely contained contempt. The casual mentions of women who had "wronged" and "attacked" his "personhood". The complete absence of social proof; no friends initiating contact, no professional colleagues conducting welfare checks, no evidence of reciprocal human relationships requiring maintenance.
He increasingly mentioned his campaign running for Senate in NSW, but I would later learn that Brodie's political aspirations were as peculiar as they were grandiose. He had founded something called "the Progress Party," which he promoted through rambling YouTube monologues — on a political platform so deliberately contradictory it defied categorisation; a bewildering mix of seemingly contradictory positions — pro-union but offering tax breaks to tech companies, advocating for secularism while obsessing over "mega cults," supporting the republican movement while proposing partnership with China's space program. He spoke of anti-war platforms while using militaristic language, anti-poverty initiatives alongside deregulated housing schemes. He explained in one video:
In hindsight, the inability to place him ideologically wasn't "a good thing". It was a warning sign of someone creating a personal political reality where he alone defined the parameters, where consistency and coherence were less important than the performance of intellectual superiority.
But I didn't watch those videos until it was too late.
I was too busy intercepting increasing numbers of WhatsApp messages. Each one a small incursion of sexual innuendo sliding repeatedly into my notifications. Constant monitoring of my movements.
By the end of that first week, increasingly frequent:
Then messages throughout the day monitoring my movements:
The message arrived like a border guard's demand for papers as my car crept from the driveway for work, for groceries, for the simple audacity of existing beyond his surveillance perimeter.
He had transformed our shared entrance hall into a human checkpoint, complete with rocking chair, laptop, and perpetual coffee. From this self-appointed customs post, he monitored every departure with the studied casualness of someone who had mistaken stalking for conversation.
I found myself crafting elaborate exit strategies, leaving earlier each morning when the house still slept in darkness, returning later each night when his vigilance might have finally exhausted itself. Each departure became a small negotiation with freedom, a careful calculation of routes and timing designed to slip past his observational dragnet.
The absurdity wasn't lost on me: a grown woman planning escape routes from her own front door, treating her home's threshold like a contested border crossing. Yet there he sat each morning, positioned with the territorial certainty of someone who had claimed jurisdiction over my movements, transforming the simple act of leaving for work into an interrogation waiting to happen.
Again and again…
The question carried the weight of accusation disguised as playful curiosity — the tiny red circle pinned on the WhatsApp tile became a digital ankle bracelet that followed me beyond the physical boundaries he'd established. Each message a reminder that even when I'd successfully navigated past his checkpoint, his surveillance continued to travel with me, passenger in my own car, companion to my own thoughts.
My instincts fired warnings I couldn't yet articulate besides my own internal screaming '*** leave me alone!'. I found myself calculating exit routes, timing movements, implementing physical security protocols without naming them as such.
That night, door locked, bathroom fan running to mask the sound of typing (acoustic emanations can reveal passwords, I'd later learn), I found his Twitter. The feed was a text and image stream of pure rage, enemies listed, conspiracies catalogued, revenge promised.
Pinned to the top:
I began scrolling through the Twitter account and found increasingly disturbing posts — violent rhetoric aimed at academic colleagues based in Sydney and Adelaide Universities he disagreed with, bound up in strange claims that all religionists suffered from mental illness, references to enemies who would "not be forgiven or forgotten."
Incident response:
My body knew before my mind could process I needed help. But I'd built my adult life on self-reliance. Two decades of solo travel, navigating foreign bureaucracies, extracting myself from dangerous situations through quick thinking and stubborn independence, going to countries where a woman alone is either invisible or hyper visible had given me a certain hardness, a protective shell built from a thousand small survivals. I'd navigated the back streets of Cairo at midnight, talked my way out of tight spots in rural Romania, learned to trust my instincts and rely on no one but myself in the far flung corners of Myanmar, Albania, India and China — where pleas for help just don't translate well.
This felt different — more insidious. The threat wasn't external; it was in my living room.
By day 8 — a tightness in my chest when I heard his bedroom door open and the coffee machine come alive — it was registering as a daily signal I needed to begin calculations about how to move through my own home undetected.
That week, I began my first steps into digital self-defence. I stared at the Twitter profile — a cold certainty settling in my stomach. A Hugh Grant look-alike with the digital footprint of someone much darker, much more volatile. A charcoal executive with burning resentments. I was coming alive to the fact that every new message from WhatsApp represented another layer in a demented neural network, spinning up tales of fiction as Dr Brodie Lang was crafting my character in his personal mythology.
I found myself in Twitter's 'advanced' privacy options, learning about location tagging, protected accounts, and who could see what.
I remember thinking how inadequate it all felt — like trying to stop a flood with sandbags made of tissue paper. Still, I methodically went through every social media account, every public profile, every place my digital-self existed or where she'd left an artifact. I changed passwords, disabled location services, removed personal details, deleted accounts. I methodically audited every social media account. It wasn't expertise yet — just the beginning of transformation based on a primal instinct to reduce my digital footprint, sensing an emergency breach on the horizon.
I began avoiding him completely, but that only seemed to intensify his interest. He started asking my housemate Maria if people from his "network in Sydney" had gotten to me, telling her I was probably out getting drunk when I wasn't around.
Then came the request that finally broke through my veneer of politeness. He must have left early that day as he messaged me from the Brindabella University campus —
The request made me deeply uncomfortable. I called him and offered to bring the envelope to him instead, but he insisted he needed the numbers immediately. I eventually gave in — another moment I've replayed endlessly, wondering if that small surrender somehow emboldened what came after.
By September 29th, I left for a Brindabella University research committee meeting at 6 AM — though it started at noon. The ladder I'd hidden in the shrubs against my bedroom window wasn't paranoia — it was an implemented failover system.
Then came that text that arrived like malware.
That evening, after just 10 days he gave notice to move out.
I felt a rush of relief, quickly followed by dread when he sent me a screenshot of the message he'd sent our landlord:
I congratulated him politely. His response: "have fun with the retards when I'm gone."
I finally broke my silence and messaged our landlord:
The next morning, Brodie rescinded his notice. The real campaign was about to begin.
On October 2nd, I found myself walking into the police station with the measured deliberation of someone conducting routine maintenance on their life's infrastructure. I requested a female officer — not from any sense of vulnerability, but from the same practical instinct that had guided me through countless bureaucratic encounters across continents. Some conversations simply required specific configurations.
This wasn't capitulation; it was calibration. The same methodical assessment that had served me well in navigating countless scenarios in foreign countries now applied to domestic law enforcement. I approached the interaction as I would any administrative process — gathering information about available resources, understanding procedural requirements, exploring institutional frameworks designed for situations that had somehow, inexplicably, become relevant to my circumstances.
I'd after all once convinced Israel's border guards that an Arabic textbook wedged between an emergency headscarf and duty-free chocolates was merely academic curiosity rather than ideological allegiance — and had learned to flip the script at the Lebanese crossing with the precision of someone whose freedom of movement depended on reading the micro-expressions of uniformed authority. I was simply applying those same negotiation skills to Australian legal protections. This was due diligence, not desperation. I told myself I was conducting reconnaissance — mapping the terrain of available options with the thoroughness of someone who had always believed in understanding all available systems before they became necessary. The fact that they had become necessary was merely an operational reality requiring tactical adjustment.
A female police officer materialised and ushered me into a meeting room. I showed her the messages and samples of the disturbing Twitter content. I took mental note of the peaking of police interest when the phrase "he's got some extremist views" fell out of my mouth. The officer left the room and returned about 5 minutes later, handing me a blank Personal Protection Order (PPO) application and walked me through the process.
In the following days, I stayed at a friend's vacant house across town, unable to face returning to my own house. On October 4th, I went to the Magistrates Court, obtained legal aid, and was granted an interim PPO.
When the magistrate asked me why I hadn't simply confronted Brodie directly about his behaviour, my answer was immediate and unwavering: I was terrified, based purely on the content of his Twitter feed which evidenced an individual on a relentless war footing with people whose lives happened to intersect with his. I showed the court examples of his explosive online persona.
The magistrate accepted my reasoning. She understood that approaching someone who publicly catalogued grievances and spoke of permanent enemies wasn't just inadvisable — it was dangerous. The digital footprint I'd discovered painted a portrait of someone for whom perceived slights became obsessions, where reasonable proportional responses had long since been replaced by a barrage of retaliatory strikes.
The Magistrate explained the PPO would be served by an AFP officer in the next few days and would explicitly prohibit Brodie from contacting me directly via WhatsApp. At this point Brodie had not actually done anything to me — his Twitter account was disturbing, yes, a red flag, absolutely — but nothing that directly targeted me aside from a single Tweet with a photo of the keep-cup I gave him and a slightly creepy caption, '…I lover her.'
Even as I left the courthouse with a partial solution, I knew Brodie would see this not as a necessary boundary but as the ultimate betrayal — proof of the conspiracy he'd already begun constructing in his mind.
But the part I wasn't expecting to transpire was that somehow, Brodie already knew, prior to the order being served. That same day, he tweeted:
How did he know I'd been to court? The order hadn't been served yet.
The question consumed me like a virus, corrupting every memory of those days. I dialled the police non-emergency line with trembling fingers, my voice barely steady as I explained what I couldn't understand: somehow, Brodie knew exactly what I'd done.
The AFP dispatcher's response — a casual dismissal:
"Maybe he just knows someone at the court who saw you there and told him."
The suggestion landed like a physical blow.
Someone at the court? I'd been extraordinarily careful, arriving early when the building was nearly empty, speaking only to the duty solicitor, court officials and the Magistrate. The idea that court personnel might be gossiping about PPO applicants to potential respondents seemed not just unprofessional but impossible.
"That can't be right," I insisted. "I'm afraid he may have me under some type of surveillance."
But Brodie's knowledge wasn't just accurate — it was intimate, precise, mocking. His next tweet that evening revealed the true depth of his surveillance capabilities:
The phrase "just for mis en scene" — the deliberate arrangement of visual elements in film or theatre. He was treating my desperate plea for help as a performance, my choice to speak with a female officer as a theatrical device designed for dramatic effect.
How did he know I'd been to the police, that I'd requested a female officer? That specific detail wasn't public information, wasn't something visible to casual observers — I'd not informed a single person. The precision of his knowledge suggested something far more sinister than coincidental courthouse gossip.
The walls of my home, my car interior, the oxygen I breathed felt compromised. And the technical possibilities multiplied in my mind, each scenario more invasive than the last.
The police's casual dismissal — "not much we can do about Twitter" — revealed the first crack in my faith in institutional protection. Here was documented evidence of surveillance, of intimate knowledge obtained through unknown means, and the response was bureaucratic shrugging.
How did he know I'd been to court? I dialled the police non-emergency line again and told them I couldn't explain his knowledge of what I'd clearly done — I'd gone to police, requested a female officer and then gone to the court. The same AFP at the end of the enquiry line dismissed my concern, suggesting "maybe someone you know has told him."
That night, I barricaded my front door with furniture only to remove the furniture after an hour, when a more reasoned version of myself decided not to provoke him further. He was still, technically, a legal resident of the house. But the barricade itself was telling. A supposedly worldly and resilient woman was locking herself in her own home, afraid of confronting a housemate.
Persistence in the network
The Tweets multiplied like viral code. Each tweet precisely crafted — unhinged enough to avoid legal consequence, specific enough to destroy relationships and plant seeds of doubt in minds of my housemates. He understood the gap between social harm and legal harm, exploiting it with philosopher's precision. Brodie painted himself as the reluctant whistleblower and victim at the same time.
I am politically exposed. It's not impossible that she's being paid under the table or offered sexual favours etc.
This is the kind of woman one is afraid to disagree with or reject due to histrionic/NPD externalising symptoms.
Each claim more outlandish than the last, yet each landing like a physical blow. He was creating a version of me that bore no resemblance to reality, but doing it so publicly, so confidently, that I began to wonder if others might believe him.
I observed the gradual uptick in his Twitter followers.
I filed a complaint with the e-Safety Commissioner and advised my landlord and my two other housemates to report the messages they were receiving via WhatsApp, which Brodie was also posting via screenshots on Twitter — rather than engaging directly. The landlords filed an additional report with ACT Region Crime Stoppers.
Looking back now, I can see I was in a state of perpetual hypervigilance — not just of what Brodie might do next, but of who might believe him.
Had he been in contact with my colleagues and friends at Brindabella University — or would they see these posts? What about the people I worked with, particularly Tyler? Would they associate me with these wild accusations? The shame of merely being connected to such public ranting, let alone being under the spotlight, was overwhelming.
The next day brought a new level of violation. Brodie tweeted at the ACT Police Twitter account with our full address:
I called police again and asked them what happens with reports made to their Twitter handle. They told me they periodically keep an eye on it, but not to worry too much about it.
My landlord and her husband confronted Brodie about posting the house address online. In a message on WhatsApp they wrote:
Brodie replied:
The tweets continued, dozens per day, each more unhinged than the last:
Her work colleagues know, her academic supervisors know — I've been in touch with them and I'll be subpoenaing them
She was giving me a string of gifts and effusively perseverating for a full two weeks daily about her supervisors, her colleagues and housemates.
#April_Sinclair is a serious problem and has some kind of personality disorder.
There it was again and again — my real name (which I've changed here too, for obvious reasons), transformed into a hashtag for his hundreds of followers. The doxing had begun, though I didn't yet have language for what was happening to me.
When I brought a pile of printed screenshots amounting to roughly 35 pages to the police station, the officer squinted at them like they were written in a foreign language.
"Doxing." "D-O-X-I-N-G." I had to spell it phonetically to blank-faced officers who treated my evidence — meticulously organised screenshots, documented URLs — like incomprehensible code.
"Sorry, what is doxing?"
"Doxing means releasing someone's private information online to incite harassment."
The word felt ridiculous in my mouth, made-up, like trying to report that someone had cast a spell on me. I spelled it out slowly as my attention turned to the singular task of not letting myself cry while watching him hunt and peck at his keyboard.
"Sorry, Ms Sinclair — doxing?" The stack of printed evidence just sat there on my side of the counter — rapidly established as dismissible based on the examination of page one by the attending officer — the entire contents of zero interest to Police.
I explained it again, watching confusion cloud his face.
"So he's just... telling people who you are? On Twitter?"
The dismissive tone made clear how little this violated his understanding of harm. How could I explain that each exposure of my details coupled with Brodie's elaborate profiling and psychological evaluations opened up real possibilities of what any unstable person among his followers might do with my coordinates?
His Twitter following grew daily. The tweets evolved into elaborate theories about my supposed personality disorders, my drug connections, my history of "targeting" men. He live-tweeted his analysis of my psychology to an increasingly engaged audience:
She has extensive connections to Islamic extremists at Brindabella University [names]. I've documented her meetings with known radicals. This goes deeper than just one sick woman — there's an entire network protecting her. Stay tuned for my full exposé.
UPDATE: Have discovered she previously lived in multiple share houses where similar patterns emerged. Am in contact with former housemates who confirm erratic behaviour, likely drug use. Building comprehensive dossier for court.
Halfway through October and a response showed up from the e-Safety Commissioner. It arrived after weeks of Kafkaesque correspondence — a bureaucratic dance that epitomised the institutional schizophrenia of digital harm response.
Jordan from the Cyber Abuse Team had requested specific URLs. I'd obediently provided twenty-two of them, each a breadcrumb in Brodie's campaign of digital terrorism. Sorted under these subheadings I'd documented each with a screenshot and a matching URL:
- Explicitly naming me
- Email image with my full name
- Thread soliciting information about me
- Screenshot of messages to people I know about me
The response:
April, if you have not already done so, we strongly recommend that you block the account on X and avoid looking at the material if it is causing you distress.
The official correspondence went on…
The scheme is not intended to regulate reputational damage, hurt feelings, bad online reviews, or strong opinions.
Moving forward, they urged me, with earnest administrative precision, to maintain a meticulously annotated portfolio of evidence: screenshots catalogued, URLs documented, timestamps preserved where possible. Yet simultaneously, with equal institutional gravity, they stressed that I must refrain from looking at the material itself (for my own psychological wellbeing, obviously).
The absurdity was staggering. I was expected to become a forensic archivist of my own destruction while wearing a blindfold, collecting evidence of systematic harassment without witnessing it, documenting threats without reading them. How does one screenshot content they're advised not to view? How does one timestamp abuse they're counselled to avoid? The contradiction revealed the fundamental inadequacy of systems designed by people who had never been hunted through digital channels, policies crafted in the comfortable abstraction of theoretical harm rather than lived experience.
Twitter's response was even more formulaic — twenty-two identical auto-responses:
Twenty-two URLs provided. Twenty-two examples of targeted harassment. The response: "We appreciate the material may be upsetting, however it does not meet the criteria."
The platform's algorithms were calibrated for engagement, not safety. With not a single successful takedown request — I was like a firehose.
"Go and kill yourself" — not a direct threat
"Janis: sick and criminally dangerous" — that's speculation, not defamation.
Each rejection confirmed what was happening didn't matter.
Early October, Brodie was gloating on Twitter that he was scheduled to give a presentation at a philosophy conference on December 6th. This explained why he was reluctant to leave Canberra entirely. I made the difficult decision to contact the conference organisers:
A conference event organiser called me the next day. He told me the committee had received corresponding concerns from academics at Sydney University and were increasingly alarmed by reports of online harassment campaigns against former colleagues. I was informed that arrangements had already been made for university security to be present during Brodie's potentially provocative and offensive presentation. However, given what I'd brought to their attention — the personal nature and the potential impact on one of Brodie's targets in their own home — they would meet to discuss rescinding the invitation entirely.
On October 11th, the conference committee rescinded Brodie's invitation. He, predictably, posted their email and his response on Twitter:
I need to know who specifically complained and what exactly you are referring to in the case of my on-line activities. I consider your actions to be unprofessional, libellous, and defamatory and to constitute harassment of my person... Please be forthcoming in the provision of information.
Also Indicate: If you have had any contact regarding this matter by persons who have behaved criminally in the recent past, including a one April Sinclair (who is a mentally ill individual who has committed legal systems abuse and criminal harassment of my person including domestic psychological abuse in collusion with others.)
The tweets grew increasingly vicious through November:
Nasty, worthless little sociopath shit-person.
Horrifying little freemasonic, tattooed sociopath-weirdo. Should have been jailed for abuse of systems long ago. She should definitely kill herself. What a nasty, disgusting, abusive, bitter, twisted, lying relational aggressive sicko.
And later:
There's a pattern of behaviour, and the aggression and lies are brazen. Definitely someone who should suicide to save everyone else pain and grief.
And finally, direct:
I called the police.
I called the Domestic Violence Crisis Service.
I called 1800 Respect.
I called Relationships Australia.
Each time, I was told there was little that could be done.
The worst part wasn't the abuse itself, it was the isolation it created. The crisis counsellor at 1800 Respect suggested I ask my closest friends to monitor and screenshot Brodie's tweets for me, to spare me the psychological damage of seeing them myself. It seemed like good advice at the time.
But my friends weren't prepared for what they saw. The sustained venom, the explicit calls for my suicide, the distorted claims about my mental health and character — it was too much. One by one, they became distant, uncomfortable with being drawn into something so toxic.
"I can't do this anymore," one friend wrote. "It's affecting my own mental health. I'm sorry."
Another simply stopped responding to my messages.
Another messaged me alarmed that I'd asked them to scroll through Twitter's gutter as Brodie had furnished his newsfeed with 100 ways to kill yourself.
A third suggested, gently, that maybe I should just "let it go" and "stop engaging" — as though documenting abuse was the same as perpetuating it.
The isolation deepened. Each day brought fresh automated responses from Twitter stating that Brodie's posts did not violate their terms of service.
Meanwhile, Brodie's efforts to isolate me further intensified. He began posting screenshots of WhatsApp conversations with my landlords, who lived in South Korea and relied on me to manage the property. In his tweets, he informed them that I was so mentally ill that I didn't recognise the filth I was living in.
The psychological manipulation was surgical. He positioned himself as the rational academic forced to witness my supposed pathology.
The shame was paralysing. My landlords couldn't see for themselves, couldn't verify his claims against the spotless bathroom I maintained. The rental crisis in Australia was worsening daily — if I lost this house, where would I go? He had already intervened in my work relationships, humiliated me in front of senior colleagues, and now he was destroying the trusted relationship I had with my landlords.
I remember thinking, with terrible clarity — There is nothing left for him to destroy.
Except Tyler. The thought kept returning — what if Brodie discovered him. The mental image of Tyler receiving subpoenas, of having to read Brodie's deranged theories about my supposed criminality, made me physically ill.
On November 14th, I attended a PPO conference at the Magistrates Court. The court sheriff found it curious that Brodie had wandered into the wing of the court, and later past the discreet location where Domestic Violence and Protection order applicants like me were whisked away to, to avoid meeting their abusers. The sheriff gently asked me if Brodie had ever had occasion to be alone with my iPhone, and if I knew how to do a complete system reset… today.
As the thought sunk in that I was holding Brodie's surveillance tracker in my hand, the sheriff went about organising a car escort for me back to Brindabella University because Brodie continuing to brazenly wander around unauthorised sections of the court was a bright line crossed as far as court security were concerned.
During the conference, Brodie had even admitted to the court official that he had recorded a phone call between me and my landlord from the bathroom — something that should have been impossible unless he had placed listening devices in my room.
It was not just the revelation of potential surveillance, but the admission of it in open court, the casual way he revealed the extent of his intrusion into my privacy.
The police finally agreed to take a report mid-November, and two officers came to my home and collected what was originally 35 pages of screenshots but had expanded to 60. They promised to be in touch shortly to take a formal statement from me. I'm still waiting for that call.
By late November, I remembered the envelope he'd got me to flex and open so he could get the CSV. Brodie had escalated to accusing me of theft — the moment with the bankcard request came flooding back:
During the day, I meticulously documented every tweet, every police call, creating folders and subfolders of evidence that no one seemed interested in reviewing.
November 2024. The pre-mention hearing should have been routine.
When his voice came through the speakers — "I intend to subpoena twelve, possibly thirteen witnesses" — something in my neural architecture crashed. The therapy dog's arrival provided what psychologists call a somatic anchor. But I wasn't having a breakdown — I was having a breakthrough. Those thirteen witnesses represented everyone who mattered in my professional world. He would force them all to participate in my public destruction.
The thought of one person — Tyler — seeing Brodie's tweets, of having to explain the surreal nightmare my life had become over the last 3 months, filled me with a particular kind of anguish. There was something about his quiet competence, his unflappable nature that made him feel like an anchor point in my increasingly chaotic world. He was father-figure and intellectual mentor rolled into one — someone whose respect I valued more than I cared to admit. Tyler — not his real name either — held authority without wielding it like a blade and he represented shards of my old self I was desperate not to lose completely: the image of myself as competent, professional, worthy of respect.
If Brodie destroyed that…
The decision to leave Canberra crystallised. Not as escape but as recognition: the legal system had become another vector for abuse.
November 27th, I finally reached out to the Victims of Crime service:
You have been recommended to me by the legal aid at the ACT Magistrates court. I currently have a PPO that was served on xx October against respondent Dr Brodie Lang.
Since that time, I have been unsuccessful in several requests for police assistance to enforce both the Personal Violence Act (section 98/98) and the PPO itself. The respondent is currently regularly (at least once every 2 days), publishing online my name and address at Twitter handle @DrBrodie_Lang73 to over 1000 followers, and accompanying the identifying detail with terrifying unhinged contempt.
This has been a harrowing 10 weeks since having known the respondent and has included a visit from paramedics on Nov xx as my Doctor was concerned on a Telehealth appointment that I was a suicide risk.
That night, I discovered Wireshark — a network analysis tool that let me see the invisible currents flowing through my digital life.
I had no real understanding of what I was looking at: the streams of packets, the colourful visualisations of network traffic. But there was something reassuring about being able to see the invisible currents flowing through my home network, about having some small window into what had previously been hidden.
I spent hours that week watching video tutorials, learning basic packet analysis, trying to understand what normal network traffic looked like so I might recognise when something was amiss.
Was he monitoring my online activities? Could he see when I was researching domestic violence resources? Was my search history exposed to him?
These technical questions gave me something concrete to focus on amid the growing fear. The challenge provided something my fracturing psyche desperately needed: concrete problems with verifiable solutions. Unlike human behaviour, packets followed rules. Unlike legal systems, networks could be secured.
The next night came another discovery — all my car tyres, slashed in darkness. The visual carried the signature of crowd-sourced hatred. Not necessarily Brodie's own hands, but the inevitable physics of his campaign: amplify the target, broadcast the coordinates, let the network complete what words began. The paralysis that gripped me was pure fear and hopelessness against the moment when the digital became physical, when the screen bled into the street.
All those weeks of watching his Twitter following grow, of seeing my name and address shared with strangers, of documenting threats that police dismissed as "just words on the internet." Here was the translation — the perfect crime of modern harassment, algorithmic distance wrapped in plausible deniability. Who can prove which follower cheering in the shadows picked up the knife?
I stayed there on my knees longer than I should have, staring at the evidence of how quickly virtual becomes visceral. The violation wasn't just in the slashed rubber — it was in the knowledge that someone had stood here, in the quiet of my neighbourhood, and decided I deserved this particular flavour of fear.
The following morning, the Victims of Crime service called. I'd been assigned a case co-ordinator, Brenda, who was willing to help me raise a charter concern with the AFP for lack of action. Her voice was professional but warm:
"What you're experiencing is real abuse. Sometimes the only way to stop it is to remove yourself entirely. Have you considered relocating?"
The word hung between us — relocating. Such a clinical term for tearing your life out by the roots, for admitting defeat so complete that geography itself becomes a last defence.
The next time I saw Tyler, I asked him to walk me to my car.
I recall my mind elaborately encrypting what was for a brief moment a plaintext revelation that Brodie had sent Tyler… something.
It didn't matter. My flight to Pandanus Reach was booked for the following morning, but the words wouldn't come.
At my car, he offered a casual wave. "See you next week."
I nodded, memorising his face in the real world, and reality of my own in the internet's fake one.
The plane lifted off from Canberra airport on a Tuesday morning so ordinary it felt surreal. Below, the city shrank to a circuit board of streets and buildings — seven years compressed to a view that fit in an airplane window.
I pressed my forehead to the glass and watched my life disappear.
Pandanus Reach airport was a shock of heat and moisture. No job, no car, no plan beyond survival. I found an AirBnB where I could watch storm clouds gather over the Timor Sea during monsoon season's full assault. Pandanus Reach in wet season — chosen for its distance, 4,000 kilometres from everything familiar. The city felt like a frontier outpost where anonymity might be possible. Pandanus Reach in the wet season — I'd chosen it precisely because it felt like the edge of the world, the furthest possible point from Canberra without leaving the country entirely. Shop fronts stood empty, their windows reflecting the orange light of a sun that seemed to hang in the sky longer than physics should allow. From someone else's Monsoon Parade balcony, I could watch the lightning fork down over the harbour, counting the seconds between flash and thunder, measuring the distance to devastation.
Pandanus Reach is like nowhere else in Australia — it's Southeast Asia transplanted, a forgotten corner of Thailand perhaps, where the jungle presses against civilisation in people's backyards. Thailand had always been my backup plan — the place I'd flee to if Australia ever became uninhabitable. I'd spent enough time there to know which visa runs to make, which expat communities might absorb someone trying to disappear. But sitting in Pandanus Reach's oppressive heat, watching the nightly storms roll in from the Indonesian archipelago just to the north, I felt like I'd found a compromise. Still Australia, still technically home, but far enough from everything familiar that I might have a chance to become someone else.
I studied. Online courses in cybersecurity.
The easy friendliness of locals who'd seen every kind of human debris wash up on their shores, the perpetually displaced who drifted between Australia's remote service towns. I fit right in, just another refugee from somewhere else, carrying some pitiful secrets I couldn't share.
But Pandanus Reach wasn't Canberra. What struck me first was the strange intentional backwardness, where everyone had collectively settled on a time about fifteen years ago and decided to stay there. In Canberra, everyone was alive to cybersecurity threats. Data breaches were discussed openly and daily. Two-factor authentication was standard, and even the most technically illiterate had absorbed basic digital hygiene through osmosis.
Finding work and a place to live in Pandanus Reach was like digging through layers of rejection to unearth possibility. Applications, interviews where I carefully edited my story, explaining my presence in Pandanus Reach with vague references to "seeking a change" — to complete bullshit such as a desire to be closer to family up here in the territory.
When I was finally offered an administrative position, I was relieved to be back in bureaucracy. But the region's technological landscape was like stepping back in time.
It was like discovering that an entire population had somehow missed a major historical event, a parallel universe where the Optus and Medibank breach never happened, where the phrase "password123" wasn't an obvious punchline. The mention of multifactor authentication drew blank stares from colleagues who looked at me like I was dreadfully unwell and completely unaware that geography provided a buffer from digital threats, and that it was a well-known fact that cybercriminals respected the regional border.
I found myself biting my tongue constantly. When colleagues discussed their "password recovery" systems — keeping all their passwords in an unencrypted Word document on their desktop — I wished I was home, where my interest in cybersecurity could have passed for unremarkable, even admirable. Here it was arcane, irrelevant, almost antisocial… and useless.
I began to wonder if I was the problem. Had my experiences made me hypersensitive to threats that didn't actually exist?
Six months into my Pandanus Reach life, I'd managed to acquire a couple of friends — but each heard a carefully crafted and edited extract from the real reason I'd fled the south. I became skilled at deflecting, at offering just enough truth to satisfy curiosity without revealing the depths of what I'd experienced.
"Relationship stuff," I'd say vaguely when asked why I'd left Canberra. "You know how it is." Or: "Work situation got complicated. Sometimes you need a fresh start."
The partial truths felt like lies, but the alternative — explaining about Protection Orders and Twitter harassment campaigns — seemed impossible. How do you begin that conversation? How do you gauge whether someone has an executable up their sleeve that shuts down the whole system… "you don't have to tell me"?
But slowly, tentatively, I began to make genuine connections.
Still, I never told any of them about the moment with the therapy dog. About the crushing shame.
Eight months into my Pandanus Reach exile, I discovered that MVIT offered cybersecurity courses. It gave structure to knowledge I'd acquired haphazardly, filled gaps in my understanding, and provided industry-standard terminology for concepts I'd discovered through necessity.
The MVIT discovery felt like alchemy. The offer to teach followed — transforming violation into prevention, taking knowledge born from necessity and using it to protect others.
The Camera: Retroactive Violation
Three months later, the call from Maria (my former housemate) shattered what little peace I'd found:
"We found something in the curtain rod of your old room… a tiny camera."
The world tilted. Every private moment retroactively contaminated. Every assumption of safety retrospectively naive. Had he watched me dress? Recorded the phone calls?
I made it to the bathroom before the vomiting started to expel knowledge too terrible to digest. But afterwards came a cold, technical fury. I kept studying.
The Podcast Performance; Ironwood
I join the Teams chat reading through the script I'd been handed the day before. The tell-tale work of an AI; a cheerful dialogue about social media wellness for a podcast segment. The irony wasn't lost on me, but I'd become expert at compartmentalising such contradictions.
"Just follow the script," was my instruction. But studying the generated conversation, I could see the shine of AI fingerprints, that peculiar flattening that occurs when nascent artificial intelligence attempts to simulate human discourse. The dialogue was coherent, tightly structured, yet utterly two-dimensional. Monochromatic in the way that only machine learning can achieve, reducing the wild complexity of human experience to statistical expectation laid down one-tok-en-at-a-time-as-the-law-of-aver-age-truth.
If you're a writer and you feed an idea into an LLM, asking it to generate extended conversation, the giveaway isn't just its coherence, it's the human authenticity that's annihilated by over-fitting. The AI renders characters as clichés, but more insidiously, it corrals the edge cases of human experience into statistical compliance. Linear regression becomes a form of existential tyranny, drawing its relentless line through the scattered constellation of actual possibility and declaring everything that falls too far from that line an outlier to be discarded.
The algorithm searches with mathematical hunger for the normative core, the statistical centre of gravity around which all experience must orbit. It cannot tolerate the roads less travelled because those paths disrupt its predictive models. Every deviation from expected patterns gets smoothed into conformity, every authentic irregularity gets weighted down until it settles back toward the mean. The character it renders becomes a prisoner of probability, reliably finding their way back to the median not through choice but through algorithmic coercion.
What dies in this process is precisely what makes us human — illogical responses to logical situations, for choosing the harder path when the easier one beckons. The AI cannot comprehend why someone might flee 4,000 kilometres rather than simply blocking a social media account, because what transpired wasn't in the fucking training data.
So it offers instead the sanitised version: wellness wisdom that assumes rational actors making optimal choices within stable systems. It generates conversations that eradicate the outliers.
I recognised this voice, having wrestled with the temptation myself while writing. The seductive efficiency of asking Claude to reword a passage, to somehow make it "better" — only to watch it drain the lifeblood from sentences that had fought their way into existence through intellectual labour too dense to be processed even by powerful GPUs.
Writing is a technology of rigour. Ideas that must be stretched over much larger scaffolding.
But here I was, about to perform this flattened version of digital wellness discourse, to perform the two-dimensional character some algorithm had conjured from its training data.
I scanned the co-host lines I was meant to deliver with breezy confidence. They were the words of a doughy doomscrolling TikTok addict who couldn't control her information sphere and the impulse to reach for her phone.
The words emerged with practiced ease, my voice carrying the warm authority of someone who'd mastered their digital environment. But internally, I was fragmenting. Each tokenised syllable felt like betrayal of myself, and every person who'd ever faced systematic online harassment, every victim whose "mindless scrolling" was actually desperate monitoring for some piece of evidence to screenshot and take to the Police.
Curate your feed relentlessly.
What a luxury, what privilege. To suggest that someone could simply unfollow their way out of targeted harassment was like telling someone to cure a tumour by thinking positive thoughts. I'd never followed Brodie's account, never engaged, never done anything but document and report and report and report his constant violations of privacy, harassment, intimidation, defamation. Each submission meticulously collected and labelled, evidence carefully compiled, URLs precisely documented with timestamps. And what did Twitter offer in return? A love-bombing campaign of automated indifference — a steady stream of identical automated responses slid into my inbox:
Identical rejections, each arriving within 47.5 hours, nicely inside the 48-hour response promise, like some perverse notification system designed to remind me that whatever harrowing experience that was arising for me, from my full name and address broadcast to hundreds of followers, fell comfortably within their community guidelines.
We have found that this account is operating within our terms of service, the platform insisted with mechanical certainty. There's no violation here. Perhaps receiving daily suggestions that you should kill yourself was merely robust public discourse.
This was just another Tuesday on Twitter. And obviously a colossal overreaction on my part.
I heard myself continue…
The lie tasted metallic. I'd turned off notifications not from choice but from necessity, to silence the sound fear makes when you understand that everyone you know, every friend and colleague whose respect you treasure, exists as potential targets in an arsenal of synthetic possibilities. Brodie's computer science background wasn't just academic credentialing; it was weaponised fluency in the architecture of deception. His demonstrated fascination with AI technology meant that any photograph could be manipulated, any screenshot fabricated, any conversation synthesised with algorithmic precision. The notifications I'd silenced weren't just alerts, they were potential vectors for manufactured evidence, deepfake testimonies, synthetic scandals crafted with the same casual efficiency he applied to his political manifestos.
My anxiety hadn't dropped; it had metastasised into a constant calculation of digital vulnerability. Every person in my professional network became a possible recipient of AI-generated "evidence" of misconduct, photographs that had never been taken, conversations that had never occurred, documents that bore my name on content I'd never written. The technology that promised creative liberation had become, in his hands, a factory for manufacturing plausible lies. Each notification carried the potential for synthetic destruction, algorithmically generated and indistinguishable from authentic documentation until forensically analysed, if anyone bothered to analyse rather than simply believe.
But worse than the lies was how easily they came, how naturally I slipped into the persona of someone who'd achieved digital wellness through simple lifestyle adjustments. The woman speaking sounded competent, balanced, in control — everything I'd once been, everything I was desperately trying to become again.
I nodded along to the sound of my own chirping voice, remembering the nights I'd fallen asleep clutching my phone not from digital addiction but from desperation, taking inventory of who I'd called that day begging for help. 1800 Respect, who redirected me to domestic violence services that couldn't assist because Brodie and I weren't in a relationship. The Domestic Violence Crisis Centre, whose well-meaning counsellors suggested I ask friends to monitor his posts for me — advice that had systematically isolated me as each friend became overwhelmed by the sustained venom. My doctor, who'd written medical certificates recommending relocation while struggling to find clinical language for technology-facilitated psychological warfare. The Victims of Crime service, who'd become my lifeline after legal aid recommended them. The court-appointed legal aid lawyer who'd expressed doubt that online abuse constituted "personal violence" in the eyes of the law. The direct line to the sergeant at the police station, who had 60 pages of Twitter and WhatsApp screenshots buried somewhere on his desk destined for the shredder, evidence that had been collected with promises of follow-up that never materialised.
Each recent call on my phone had become a monument to institutional inadequacy, a directory of well-intentioned people working within systems that hadn't evolved to recognise the harm I was documenting. The phone I clutched wasn't a security blanket, it was a desperate tether to a support network that existed in theory but dissolved in practice when confronted with the reality of systematic digital harassment.
The conversation flowed on, each exchange feeling like stepping deeper into quicksand:
"Oh wow, that's fascinating to consider, I think the best thing would be the mental health benefits. Studies consistently show correlations between heavy social media use and increased depression and anxiety. I think we'd see people becoming more present in their immediate environments and relationships."
I replied with perfect maintained cadence.
…Present in their immediate environments…. The phrase echoed with hollow mockery. I'd achieved the mental health benefits of social media's absence by fleeing 4,000 kilometres from everything I'd known. But that wasn't wellness advice anyone could offer in a cheerful campus podcast.
I continued, my voice steady despite the storm building inside.
Performative. The word hung in the concrete corridor air like an accusation. Everything about this moment was performance — me pretending to be someone who'd found balance through intentional choices rather than someone who'd learned cyber security as part survival skill, part therapy.
I managed what I hoped was a modest smile, my throat tight with unshed grief for the version of myself I'd just performed. That woman so confidently offered simple solutions to complex problems. Someone who'd never learned that digital wellness wasn't about intention but about power, about systems designed to prioritise engagement over safety, about platforms that treated targeted harassment as content worthy of protection.
That Evening: The Diary Entry
Someone who can speak fluently about digital wellness while knowing intimately that the advice is worthless for anyone experiencing systematic abuse? Someone who can discuss "mindful scrolling" with a straight face when my own scrolling was anything but mindful — it was survival reconnaissance, intelligence gathering, threat assessment disguised as social media use.
The worst part wasn't the hypocrisy. It was how easily I slipped into that role, how naturally the confident educator persona emerged. Like muscle memory from a previous life, before I learned that digital wellness is a privilege afforded only to those who aren't under active digital assault. I sat there suggesting people "diversify their information diet" when my own information consumption had been weaponised against me. Every news source, every platform, every digital touchpoint had become a potential vector for Brodie's poison. There's no "diversifying" your way out of targeted harassment; there's only documentation, evidence gathering, and ultimately, geographical escape.
After spending a couple of AI-scripted hours dispensing wisdom about digital wellness to an audience that included people who might genuinely need help, I feel like I've betrayed something fundamental. Not just my own experience, but everyone who's ever been told that their online harassment was really their own fault for not managing their digital boundaries properly.
I've learned to speak both languages now: the comfortable vocabulary of digital wellness and the harsher grammar of cybersecurity. The challenge is knowing which conversation each audience actually needs, and finding the courage to offer the latter when the former is what they're expecting to hear.
The podcast performance is over, but the questions it raised linger: How do you teach safety to people who don't yet know they're vulnerable? How do you offer genuine protection while maintaining the illusion of simple solutions? How do you honour your own experience while meeting others where they are?
I don't have answers yet. But I'm learning that sometimes the most important service you can provide is not the comfortable advice they want to hear, but the uncomfortable truths they might one day need to know.
The woman on that livestream sounded like she'd achieved something I'm still desperately seeking. I'm sitting with the dissonance of having become someone who can speak the language of digital wellness while knowing intimately that it's a dialect available only to those who've never been systematically hunted online.
The woman in the mirror looks tired. Not from the performance, but from carrying the weight of knowing that the advice I offered today — sincere and well-intentioned as it was — would have been utterly useless to the person I was eighteen months ago. That woman needed threat intelligence, not lifestyle tips. She needed platform accountability, not personal boundary-setting. She needed the law to catch up.
Epilogue
For months, I collected blank stares about what had happened — especially from the police. It would take until 2024 — after Brodie had been and gone — for Australia to formally recognise doxing as a serious harm. Following incidents where pro-Palestinian activists had exposed the identities and personal details of members of Jewish groups, the government finally acknowledged that making someone's private information public could be a form of violence.
Suddenly everyone knew the word "doxing" — television anchors, politicians, regular people discussing it over coffee. Politicians denounced the "abhorrent practice." The AFP announced task forces. Emergency legislation passed.
The word "doxing" no longer sounds made-up. It's in the parlance of criminal codification now. But I remember trying to spell it for Police officers who looked at me like I was speaking in technical jargon about imaginary crimes.
If you're experiencing technology-facilitated abuse or digital harassment, you're not alone. The skills you develop to protect yourself — technical or otherwise — are valuable and valid, regardless of how you acquired them.
Your hypervigilance is not paranoia.
Your need for security is not pathology.
Trust your instincts.
Build your defences.
Then, when you're ready, teach others to build theirs.